If you’re an aspiring social engineer, ethical hacker, business owner, or just someone fascinated by this topic (like me), you should read this article.
It will help you understand how social engineers and con men use psychology to steal your money or hurt your business.
#1 Elicitation
Imagine you hold a key position at a corporation. This means you have sensitive information about an upcoming product launch.
After work, you often have a dring at a local bar. Sometimes alone, sometimes with your collegues.
Tonight, you’re alone.
A friendly woman starts a casual conversation with you. You chat about a lot of things like movies, relationships, books, and life in general. Then you talk a bit about work but it’s harmless.
After the conversation you’re like, “This was really nice.” And you’ve no reason to believe you revealed anything confidential.
But you did.
You see, she was using a sneaky method called elicitation. It’s when you construct the conversation in such a way that the target doesn’t realize they’re giving away important information.
This is why corporations, governments, and intelligence agencies around the world train their employees to recognize and resist elicitation. But even then, there have been many cases of trained officers unknowingly giving away critical information.
Why does it work?
If we know something that doesn’t directly affect us, we are more willing to talk about it.
Jack Schaffer, ex-FBI agent and author of Truth Detector gives an example of an exercise with his students.
He asked his student to go into a jewelry store, have a conversation with the clerk, and get the needed information as if he wanted to rob the place.
By having a simple conversation with the clerk, he could learn that:
- The cameras in the store don’t work.
- Mall security officers are incapable of doing their job properly.
- The clerk won’t be a problem for the shoplifter because he was instructed not to engage with them.
- The store won’t bother shoplifting unless the loss is greater than $1200
- There are $2200 in the store right now, and the safe is broken
Based on the clerk’s information, he could steal an item that costs $1200 or less and walk away without fear of getting caught or even reported.
The clerk wasn’t aware of the sensitive information he was giving. And since it didn’t affect him directly, he didn’t care.
Of course, not everyone will reveal so much information. But your job is to collect pieces of seemingly trivial information that when combined, will help completing the big picture.
Another reason elicitation works is that it taps into a basic human insecurity: the need to feel competent and knowledgeable.
Many people want to prove they are just as smart (or smarter) than the person they’re talking to.
This instinct is why we often correct others when they say something wrong. It feels good to “set the record straight,” and once we start, we’re likely to keep going.
Communication Tips
#1 Be confident. Nothing kills the conversation more than being uncomfortable.
#2 Educate yourself. You need to know the subject you’re talking about. But mostly, you’ll ask well-thought-out questions to encourage him to talk more about his area of expertise. Make the conversation about them.
#3 Common conversation openers are the weather, asking for advice on technology, and general questions about kids, pets, and sports.
#4 When someone does a small favor for you, it makes them more willing to do you another favor.
You can thank them for taking the time to meet you, for being early, or for arriving on such brief notice.
#4 Don’t be greedy. Your goal is to get information. Yet, that shouldn’t be your sole focus because the target will lose interest.
Make the conversation a give-and-take unless you are with someone who wants to dominate the conversation. Here, let him dominate.
If you got the answer, don’t go deeper and deeper into the conversation because it can raise a red flag.
Elicitation Techniques
Appealing to their ego – This technique is simple but effective because many people take pride in their work.
They often link their identity with their work. That’s why they’ll talk freely about their professional accomplishments.
You: “You must have an important job, X seems to think highly of you.”
Target: “That is so nice of you to say, but my job isn’t that important. All I do here is…”
Or, I bet you were the key person in designing this product.
Appealing to their ego is simple and effective, but don’t overdo it or when you’re not sincere because it can turn people off.
Presumptive Statements – You make a statement that might be right or wrong and wait for them to respond.
If your statement is correct, he will agree and provide additional information.
If your statement is wrong, he will probably provide the correct answer and give a detailed explanation.
Criticize – You criticize their company, hoping he will give information during the defense.
e.g., “How did your company get the contract? Everyone knows E Corp has better engineers for that work”.
Oblique Reference – You discuss a topic related to the main issue.
For example, you discuss the catering at a work party when you want to know the type of access outside vendors have to the facility.
Questions – You ask open-ended questions to get small bits of information that will complete the bigger picture.
It can also create the illusion of authority. In conversations, we perceive the one asking questions to have more power.
Alcohol – The SE might offer alcohol to their targets because drunk people talk more than they have to.
Elicitation Sandwich – People tend to recall the first and last thing in a conversation.
So, where should you put the elicitation? Exactly. In the middle.
After you have established rapport… start with small talk… deviate the focus of the conversation to the elicitation topic… then go back to the first topic.
#2 Inside Help
Experts say that most security breaches happen because of human error but sometimes the breach is intentional.
An unhappy employee, frustrated with their company but unable to leave, can become an ideal inside asset. And managers might not aware or simply don’t consider it as a problem that they have these deeply resentful employees.
So a social engineer can target these vulnerable individuals and turn them into a “trojan horse”.
They may casually approach them in smoking areas, local cafés, or even on the same public transportation routes. From there, the conversation naturally shifts toward work and life frustrations.
If trust is built, the insider might be convinced, or even volunteer, to help:
– Installing network backdoors
– Providing legitimate access badges or codes
– Directly handing over sensitive business data
This method mirrors the tactics used by intelligence agencies recruiting foreign spies:
An operative identifies potential vulnerabilities, builds rapport, and over time, persuades the spy to betray their country.
It’s a challenging and delicate process, but with patience and the right psychological approach, it is very possible.
#3 Authority
You probably heard about the Milgram experiment and its results. A man in a lab coat at Yale University convinced strangers to harm other people.
He had no real authority to force a person to follow orders, just perceived authority.
Authority is so powerful that it overrides decision centers in the brain and shuts off our sense of responsibility.
This same principle applies in the business world. Employees are conditioned to follow the instructions of management.
So, if the employee believes that the SE is part of the management team, he will conform to any reasonable request. He might provide sensitive information and wouldn’t raise any alarms.
Another effective tactic is impersonating a security guard. Of course, putting on a uniform alone isn’t enough; true authority involves both appearance and behavior.
For example, you might casually stop an employee and ask to check their badge as part of a “routine security audit.” Very few people will challenge a uniformed security guard asking direct questions.
Authority should be embedded into every part of an impersonation. Looking the part (wearing a convincing suit, uniform, or badge) is only half of the equation. Sounding the part is just as important.
One simple trick for projecting authority during conversations is to ask questions. Psychologically, the person asking questions is usually perceived as the one holding the power.
Another powerful technique to strengthen your pretext is…
#4 Priming
Priming is when you get exposed to something like a word, feeling, or image… that influences your behavior later on without your conscious awareness.
Researchers at the University of Nijmegen ran a classic experiment to demonstrate this effect:
They divided volunteers into two groups, each taking a general knowledge test.
The first group was primed with the stereotype of professors.
The second group was primed with the stereotype of hooligans.
The first group performed significantly better than the second group.
In other words, simply activating a perception can influence how someone behaves, at least for a short time.
Now, priming is a powerful tool you can use to improve your pretext.
For example, let’s say you’re pretending to be an IT professional.
What stereotypical perceptions come to mind?
It’s a socially awkward person obsessed with technology who can fix anything computer-related, right?
This is not the case with everyone, but it’s all about perception.
To prime yourself correctly for the role, you might write down everything you associate with that stereotype:
– Appearance (messy or casual clothes, glasses, tech gadgets)
– Behavior (quiet, technical vocabulary, direct focus on problems)
– Attitude (confident when talking about systems, slightly impatient with non-technical people)
The key is that the priming works when you have expectations it is going to work. You don’t force it; you simply allow that persona to flow into your pretext. You know, it helps you on an unconscious level.
So, when you are out there pretending to be someone else, you instinctively know how to behave, and you don’t spend mental energy worrying about how you look.
#5 Working at the Company
If you can get a job at the target company, everything becomes easier.
Often, social engineers apply for a cleaning role, which has two advantages.
First, it doesn’t require any specific qualifications.
Second, it is doubtful for a business to do thorough research on applicants due to the low privileges of that job.
The irony is that the cleaners have more access to the building than other employees.
I understand that it will take a great deal of time, but the payoffs are high and low risk.
#6 Reverse Engineering
It’s a complicated technique involving a lot of planning and careful timing.
The social engineer provides help that aids the attack.
The target asks for something from SE when it’s usually the other way around.
For example, the SE impersonates someone from the IT department, asking, “Are you experiencing any computer issues?” Most likely, someone will have a problem. And the SE could help them solve it.
He/she could ask for the user’s credentials to log in remotely. Or it could ask them to visit a particular website to test connectivity, which is malicious.
A more complex strategy is to sabotage and assist. The SE causes an issue and then presents himself as someone who can solve it.
Another attack could be Introduce-Sabotage-Assist. You introduce yourself as a new member of IT, give your phone number, explaining they could call any time if they have a problem.
You’re not asking for any information, which won’t raise any alarms. The target will call the SE when the problem occurs, asking for assistance.
#7 Targeting an Individual
If you want to perform a targeted attack on an individual instead of a group, then consider the following:
- Interests
- Education
- Recent holidays
- close friends
- Family members
- What bank do they use
- What car do they drive
Here are some scenarios that are used as a basis for attacks.
If your target went to a particular school, then you can send an email like this:
Hi Ben
We’re organizing an XYZ high school reunion party for the class of 1990 and hope you can join us.
We’ve set up an account on http://www.fakeschoolreunion.com where you can rsvp.
Also, we uploaded pictures of everyone back then.
Sorry if you find them embarrassing.
Hope to hear from you soon.
Another email might include a malicious PDF file based on where they shop regularly.
XY is offering 50% off all products! Please print off the attached voucher and bring it to the store.
Pick up lines
As we have seen in many cases, a social engineer can hijack accounts, steal identities, or infiltrate corporate offices. They use pick-up lines to encourage communication with their targets.
Here are the most common ones:
I’m stuck in X place, and I lost my wallet. Can you wire some money?
The SE probably hacked a friend’s Facebook account and sent the message pretending to be him. He might say he has no money due to a lost wallet or robbery.
You should be careful and ensure you’re talking to your friend or family member. You can ask him to send you a picture of that place or ask a specific question to which he would know the answer.
Click this link
As in the examples above, the social engineer encourages the target to click a link. They might pose as your friend, work colleague, or even a company where you’re a client.
They include logos and variation links to websites such as facebookk.com, paypall.com, etc.
Example:
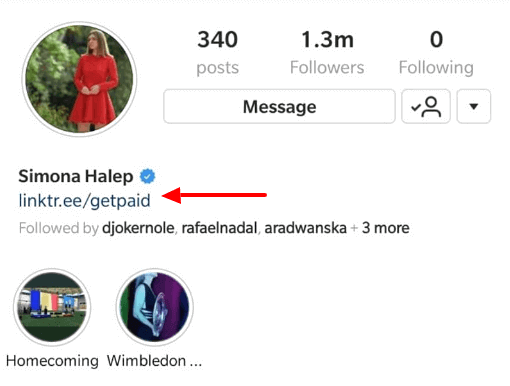
Simona Halep’s Instagram was hacked.
The attackers posted several messages, such as:
“Hey, can anybody help me? I’m stuck in Switzerland and my bank account is not working here. I need 500$, I am willing to pay 1,500$ by the weekend”.
To learn more effective social engineering techniques, you might want to read the following books:
Social Engineering Penetration Testing by Gavin Watson, Andrew Mason, and Richard Ackroyd
The Ellipsis Manual: Analysis and engineering of human behavior by Chase Hughes